Category - General
Posted - 10/01/2020 02:23pm
|
New Apple ID Password Phishing Scam, Beware!
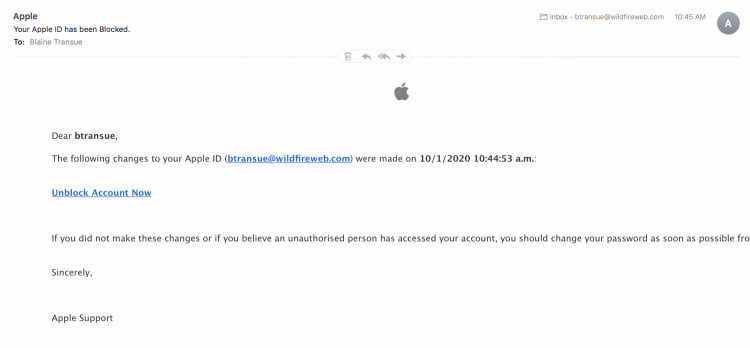
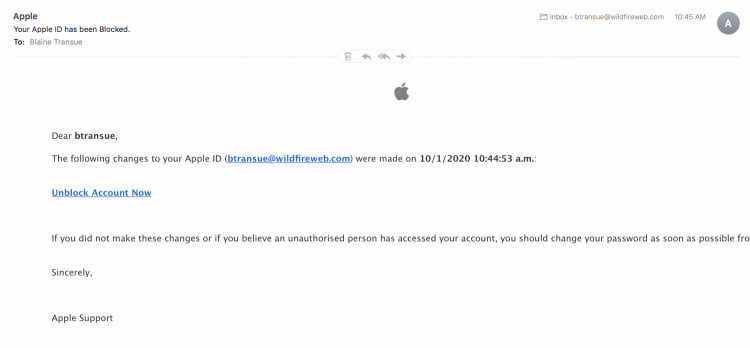
This is a new scam that just showed up in our box this morning, an email that appears to come from Apple requesting us to reset my password for my Apple ID, and I admit, it looks pretty genuine, but a few easy checks tells me this is a scam.
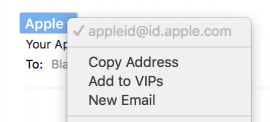
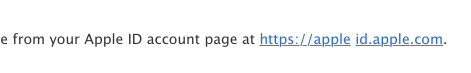
A quick Right Click on the Sender's Email address shows something that seems suspect, i.e., Apple sending support mail through a sub domain (appleid@id.apple.com) Could happen, but not usually their approach, so let's look at something else.
If I look down into the body of the email I see a link to "Unblock Account". Again, maybe it's legit, but not what Apple usually does. First Clue, they wouldn't send you a link to "Unblock Account". Password Reset link maybe, but "unblock" no. Still, if you're new to Apple, you wouldn't know that, so let's look a little farther and just see where that link they want me to click goes.
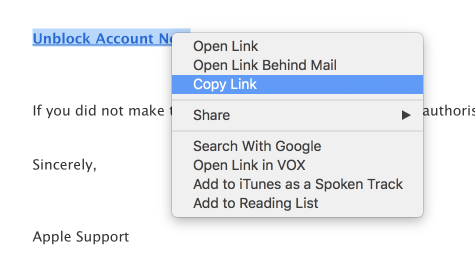
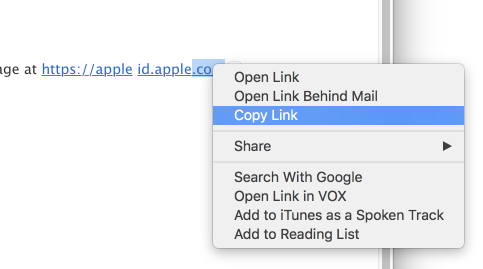
Right clicking on the link reveals a contextual menu where you can select Copy Link. A quick copy and paste into my text editor reveals something new.
https://languid-heartbreaking-earwig.glitch.me/
Ok, by this point I know it's a scam as the referral link obviously has nothing to do with Apple, but if I was still uncertain, there are other clues this didn't come from a multi-billion dollar enterprise.
For instance
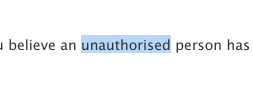
in the copy, the word Unauthorized is misspelled
They also say, from your Apple ID Account Page
Well, if you have an Apple ID, you know there is nothing Apple refers to as your Apple ID Account Page, but again, you wouldn't know this necessarily.
Another subtle clue is the visible link itself, https://apple id.apple.com. 1) it just doesn't look right, it uses apple twice and there's a space between apple and id. Ask yourself, Would Apple do that? No, if anything the prompt would be a Reset Password graphic or perhaps text link, but it wouldn't be an ugly, redundant visually broken link, no, never.
Right clicking on that link to bring up the contextual menu and copying and pasting the link in my text editor reveals, surprise, the same bogus link as before.
https://languid-heartbreaking-earwig.glitch.me/
Still not convinced, dig a little deeper
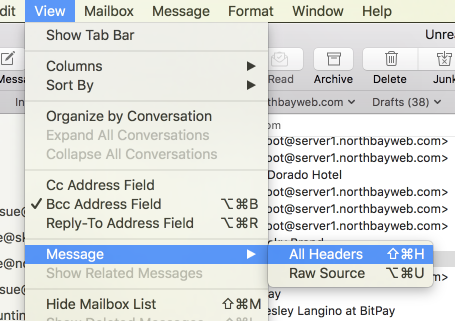
If I look at the message headers I'll see more information about where this email came from. In Apple Mail I can select View > Message > All Headers. This will display the full "header" (think of it as a path) of the currently selected email.
Viewing that header looks like this and contains all the information about the "path" of this email. Where it came from, what servers it went through, etc.
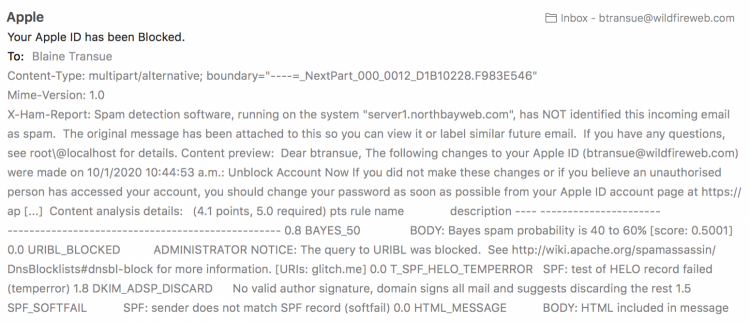
Looking through that header I see signs that things are off. Nothing looks quite right actually. Tests that would easily pass on Apple's servers fail below. For example, something called a URIBL query was blocked by the outbound server, why? When the servers "talk" to each other to establish and test the connection, the HELO test fails as does the request for the DKIM record, and lastly, the sender does not match the SPF record. Even without knowing what any of these things are, you should be suspect that these types of errors wouldn't be coming from Apple's servers.
ADMINISTRATOR NOTICE: The query to URIBL was blocked. See http://wiki.apache.org/spamassassin/DnsBlocklists#dnsbl-block for more information. [URIs: glitch.me] 0.0 T_SPF_HELO_TEMPERROR SPF: test of HELO record failed (temperror) 1.8 DKIM_ADSP_DISCARD No valid author signature, domain signs all mail and suggests discarding the rest 1.5 SPF_SOFTFAIL SPF: sender does not match SPF record (softfail)
If you look a little farther in the Header you'll see something else that should make you feel confident this email didn't come from Apple, but actually from China.
Received: from server1.northbayweb.com by server1.northbayweb.com with LMTP id +PBhFM0Vdl/RDQAAKNehTQ (envelope-from <appleid@id.apple.com>) for <btransue@wildfireweb.com>; Thu, 01 Oct 2020 12:45:49 -0500
Received: from mta0.china-mail.ga ([104.168.250.214]:35319) by server1.northbayweb.com with esmtps (TLS1.2) tls TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 (Exim 4.93) (envelope-from <appleid@id.apple.com>) id 1kO2e6-0000ye-8g for btransue@wildfireweb.com; Thu, 01 Oct 2020 12:45:49 -0500
And if you dare, copy the link in the header and paste it into your browser mta0.china-mail.ga
If you did, I'm sure you found that it did not have any relationship to Apple